API 키
설치 단계와 이 플러그인의 전체 마크다운 가이드를 포함한 설정 지시를 복사하세요.
API 키는 조직 수준에서 역할 기반 접근 제어 (RBAC)로 관리됩니다. 각 키는 조직 전체에 역할을 할당하고 선택적으로 앱당 역할을 할당하여 각 키가 접근할 수 있는 것을 세세하게 제어할 수 있습니다.
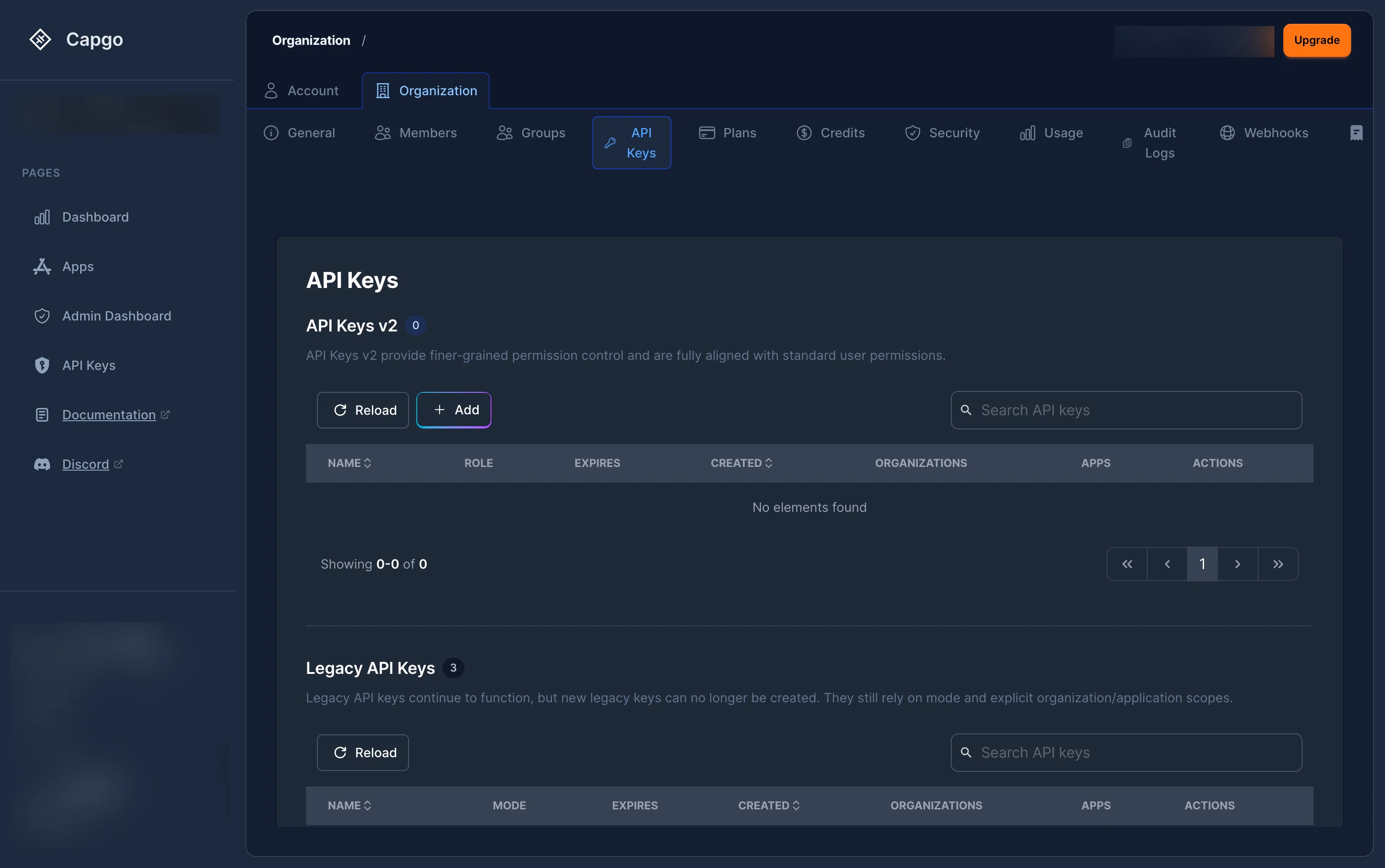
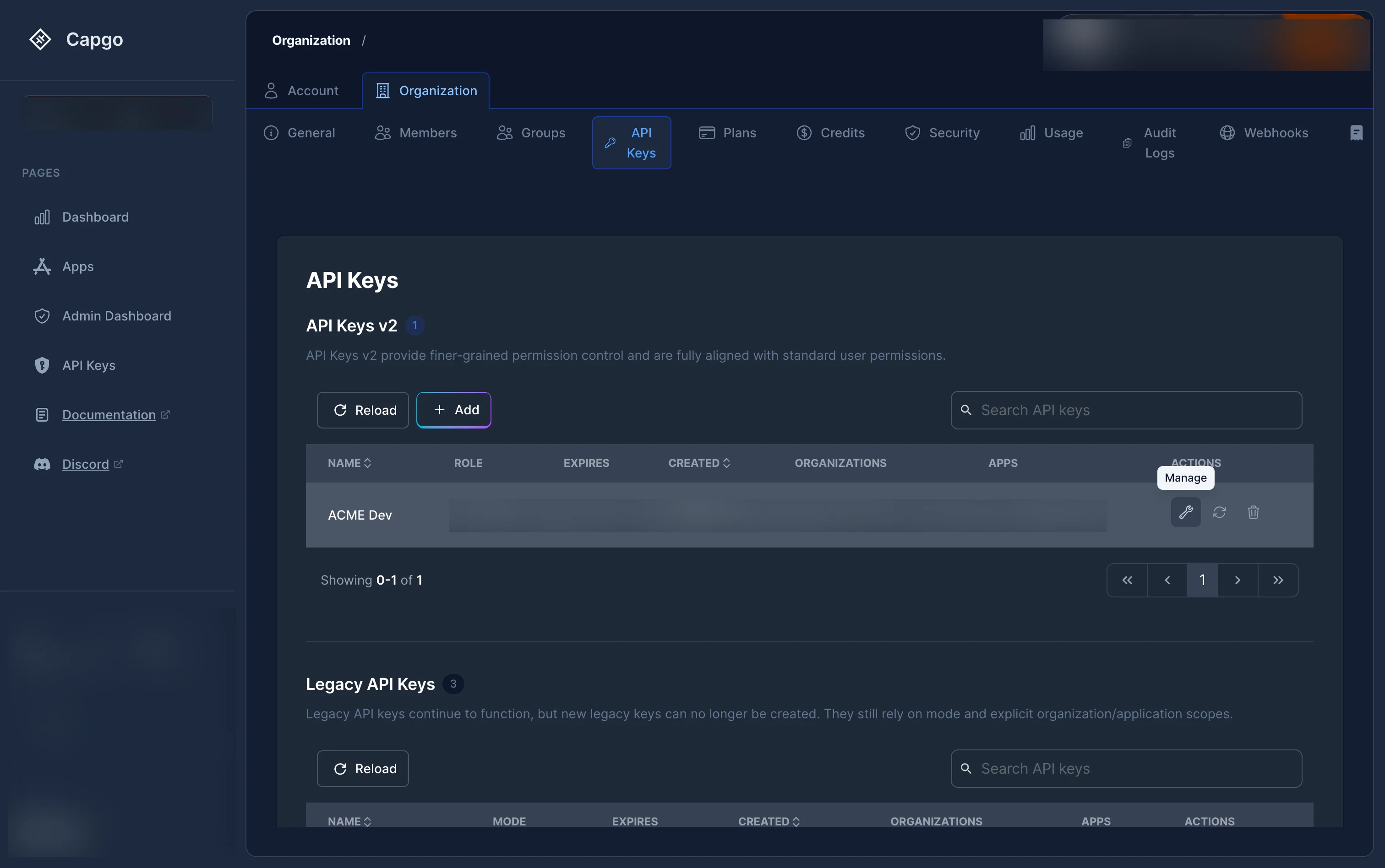
API 키는 어디에 관리되나요?
API 키 관리 위치에 대한 섹션입니다.__CAPGO_KEEP_0__ 키 관리 위치로 이동하세요. 설정 > 조직 > API 키 __CAPGO_KEEP_0__ console.capgo.app/settings/organization/api-keys.
페이지에는 두 가지 섹션이 있습니다.
- RBAC 키 — 역할 기반 권한 시스템(new)을 사용하는 키(권장).
- 레거시 키 — 단순 모드 기반 시스템을 사용하는 오래된 키(legacy)
read,upload,write,all역할 할당이 없는 항목입니다.
API 키를 새로 만들려면 어떻게 하나요?
API 키를 새로 만들려면 어떻게 하나요?-
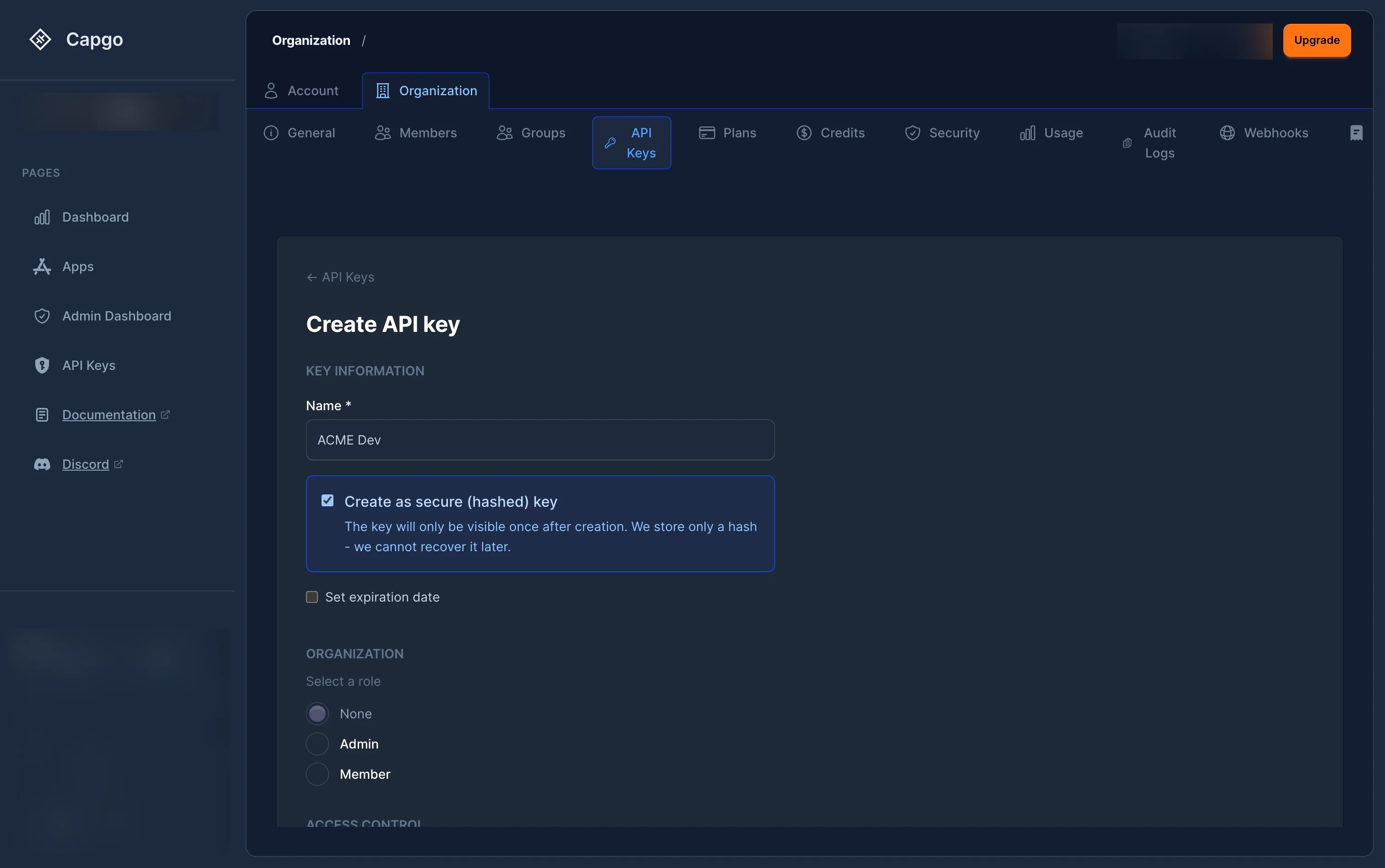
RBAC 키 테이블 위쪽의 ”+” 버튼을 클릭하세요.
-
키 정보 이름:
- (필수) — 키에 대한 설명적 레이블 (예: “CI/CD 배포”, “모니터링 읽기 전용”). 안전한 키 만들기
- (선택) — 체크하면 키가 서버측에서 해시됩니다. 평문 키는 표시됩니다. Create secure key (optional) — When checked, the key will be hashed server-side. The plain-text key is shown 한 번만 생성 후에는 더 이상 복원할 수 없습니다.
- 만료일 설정 (선택 사항) — 키가 작동하지 않게 할 날짜를 선택하세요. 일부 조직에서는 정책에 따라 필수적으로 만료 시키기도 합니다.
-
Select an 조직 역할 — 조직 전체에서 키의 기본 권한을 정의합니다. 사용자 역할 수준에 따라 사용 가능한 역할이 다를 수 있습니다.
- 없음 — 조직 전체에 대한 접근 권한이 없으며, 개별적으로 assign된 앱만 접근할 수 있습니다.
- 멤버 — 조직에 대한 기본적인 읽기 접근 권한
- 관리자 — 조직 전체에 대한 완전한 관리자 접근 권한 (모든 앱에 대한 접근 권한을 상속합니다.)
-
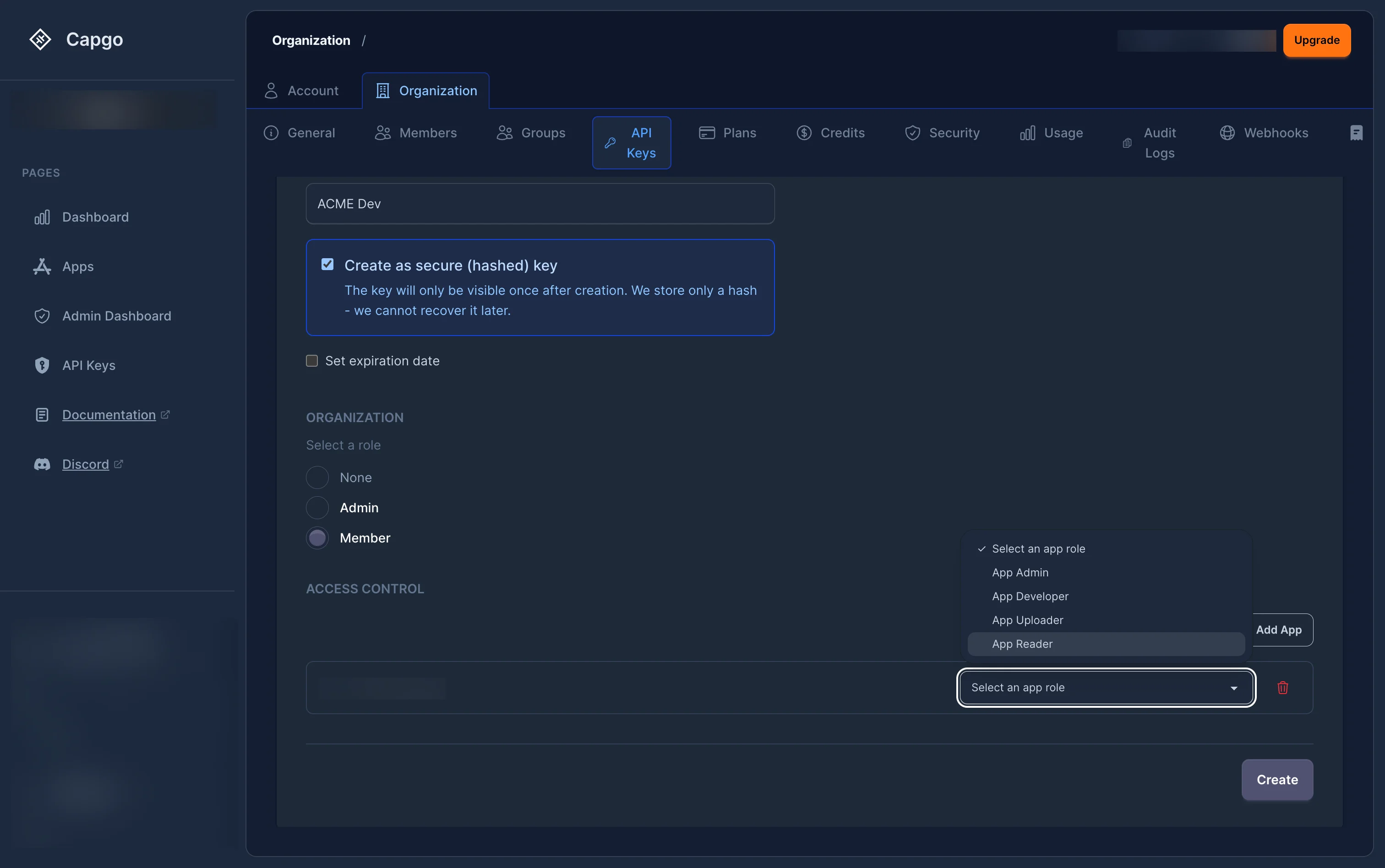
관리자 역할이 선택되지 않은 경우, 각 앱에 대한 접근 권한을 추가할 수 있습니다. 클릭:
- Click 앱 선택기를 열기 위해 하나 이상의 앱을 선택한 후 각 앱에 대한 역할을 assign하세요:
- 앱 리더
- — 앱에 대한 읽기 전용 접근 권한 앱 업로더
- — 새로운 배ंडल을 업로드할 수 있습니다. If the selected org role is not Admin, you can add per-app access
- 애플리케이션 개발자 — 앱 설정 및 배포를 관리할 수 있습니다.
- 애플리케이션 관리자 — 앱에 대한 전체 접근 권한
-
클릭 “Create”.
-
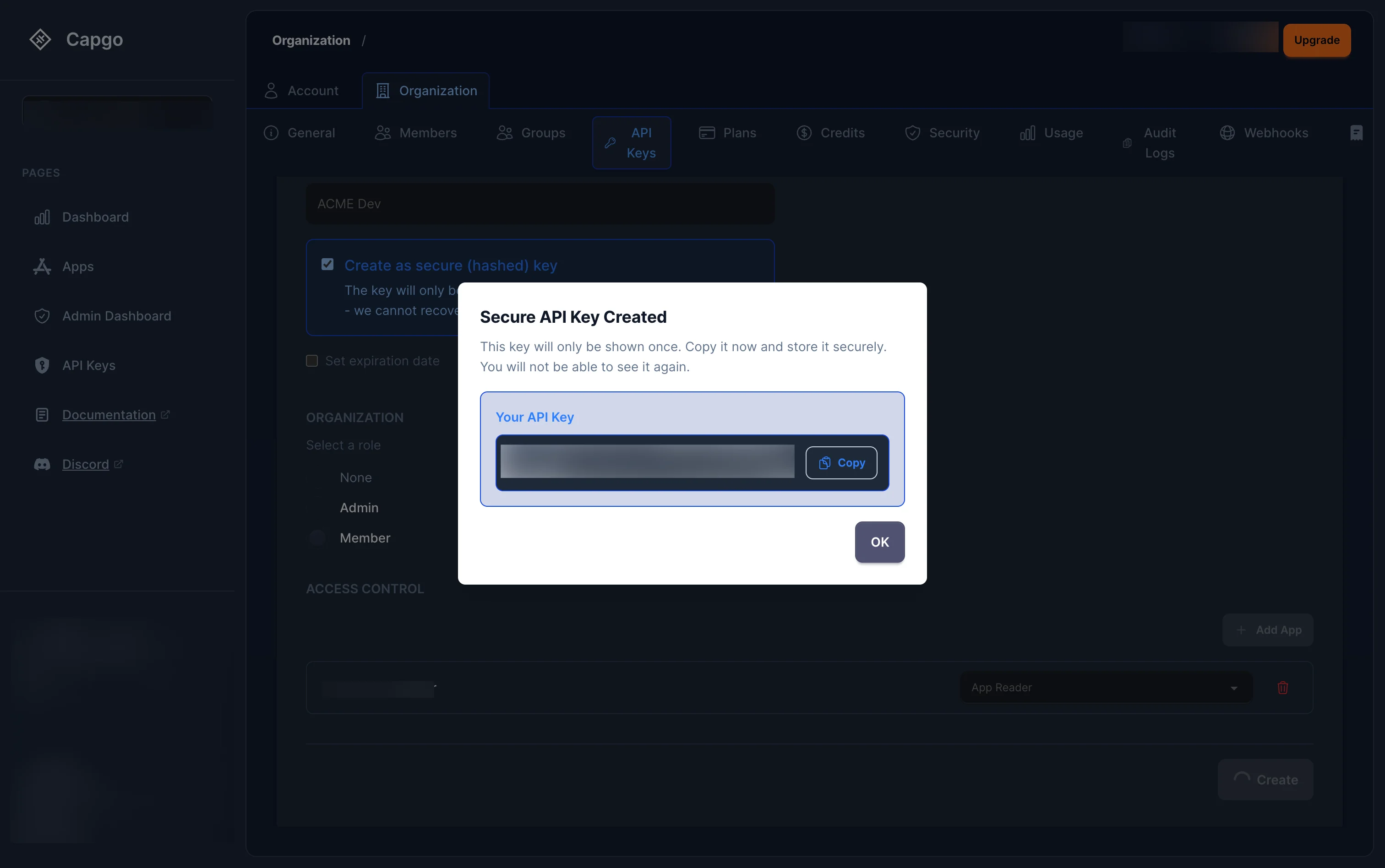
만약 'Create secure key'를 선택했다면, 평문 키가 표시될 모달이 나타납니다. 그것을 즉시 복사하세요. — 모달이 닫히면 다시 가져올 수 없습니다.
API 키를 편집하는 방법?
API 키를 편집하는 방법은?클릭 스파너 아이콘 (관리) 목록에 있는 RBAC 키 중 하나를 클릭하면 키 상세 페이지가 열립니다. 여기서 키를 편집할 수 있습니다.
- 키 이름을 변경할 수 있습니다. 조직 역할을 업데이트 할 수 있습니다..
- 앱별 역할을 추가, 삭제, 변경할 수 있습니다. ‘변경사항 저장’.
- Click the wrench icon.
(Manage) on any RBAC key in the list. This opens the key detail page where you can: Change the key name, Update the organization role, Add, remove, or change per-app roles, Click “Save Changes” 완료되었습니다.
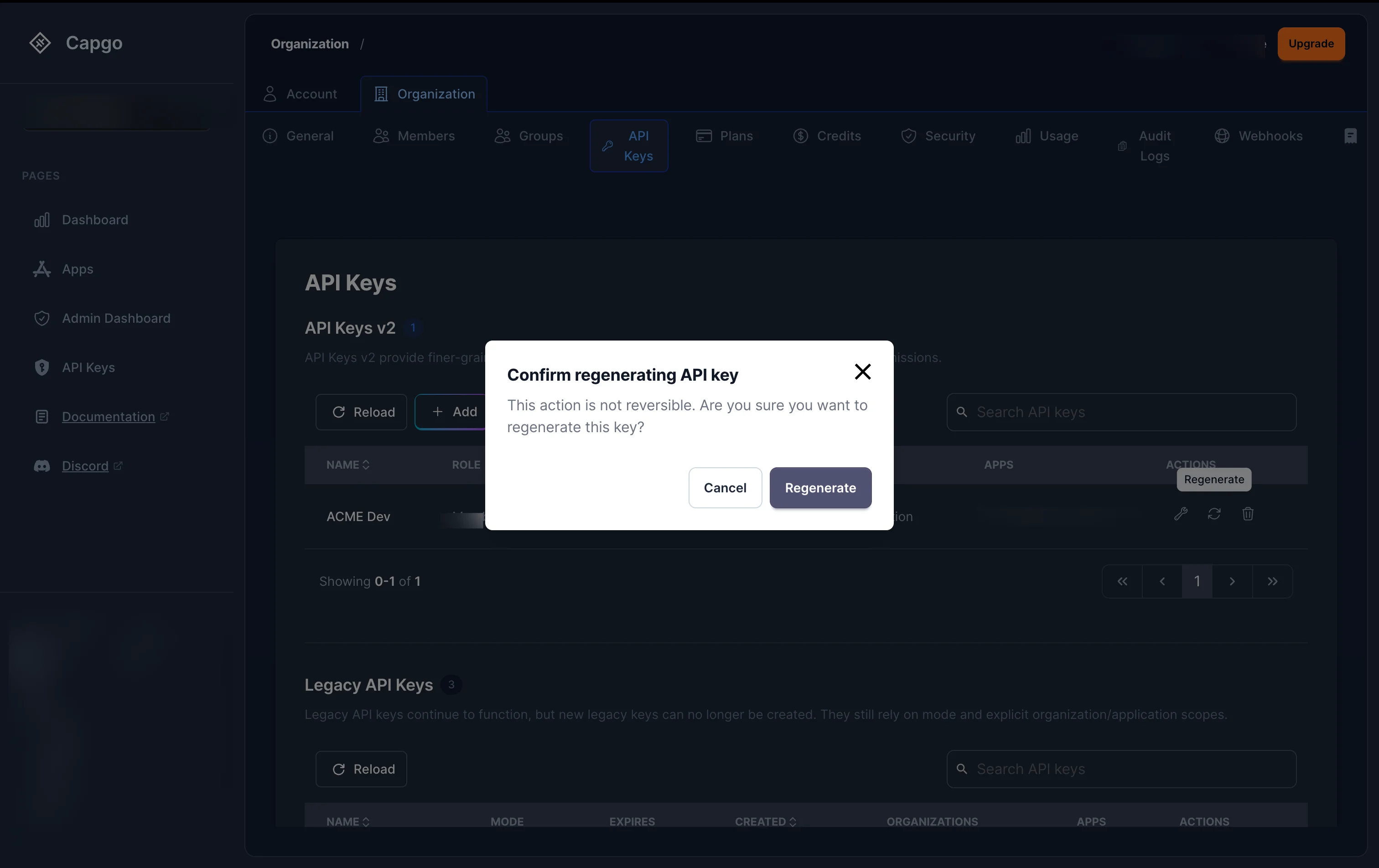
API 키를 다시 생성하는 방법은?
제목: API 키를 다시 생성하는 방법API 키의 비밀 값을 다시 생성하려면 목록에서 키를 클릭하여 새로 고침 아이콘을 클릭합니다. 목록의 키 중 하나에서 (Regenerate) 버튼을 클릭합니다.
확인 대화 상자가 나타납니다. 확인 후:
- 보안 (해시된) 키의 경우: 새로운 평문 키가 모달에서 한 번만 표시되고, 즉시 복사하세요.보안 (해시된) 키의 경우:
- 새로운 평문 키가 모달에서 한 번만 표시되고, 즉시 복사하세요. plain keys: __CAPGO_KEEP_0__ 키는 서버에서 다시 생성됩니다.
이전 키 값을 사용하는 모든 통합은 즉시 작동을 멈출 것입니다.
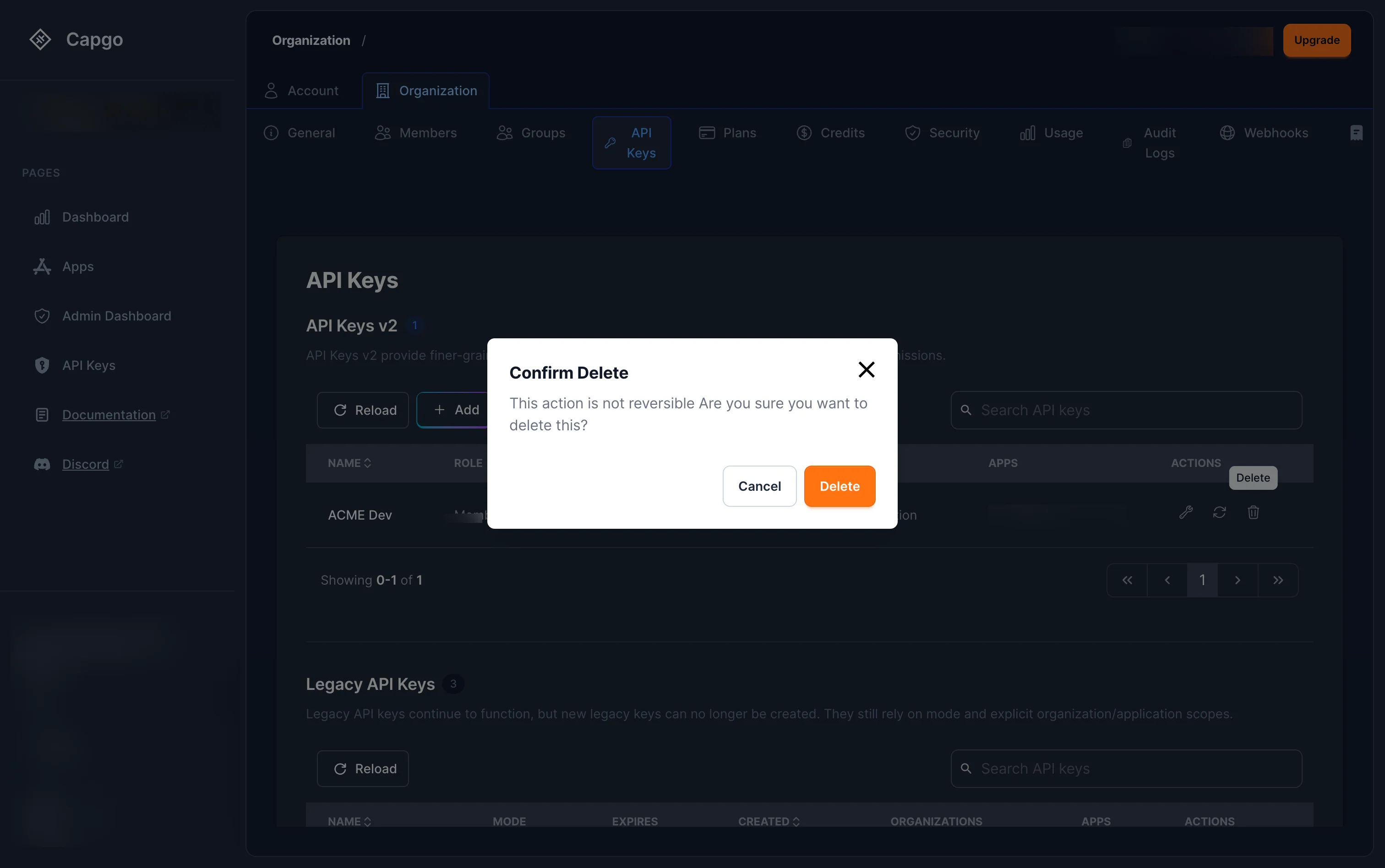
API 키를 삭제하는 방법
제목: API 키를 삭제하는 방법리스트에서 키를 클릭하고 쓰레기 아이콘 (삭제) 버튼을 클릭합니다. 삭제를 확인하는 대화창에서 확인을 클릭합니다.
키는 즉시 취소되며, 사용하는 모든 요청은 실패합니다.
기존 키
기존 키키를 보시면 역할 할당이 없는 키가 있습니다. 기존 키 이러한 키는 ( )에 기반한 권한 시스템을 사용합니다. read, upload, write, all이러한 키는 여전히 작동하지만 RBAC의 세부 권한을 받을 수 없습니다.
기존 키는 목록에서 재생성 및 삭제할 수 있지만 RBAC 역할을 추가하여 편집할 수 없습니다. 새로운 RBAC 키를 생성하고 가능한 경우 기존 키를 삭제하는 것을 추천합니다.
기존 키를 직접 관리해야 하는 경우, 여전히 console.capgo.app/dashboard/apikeys수정 페이지
